Critical LTE Security Flaw Can Remotely Inspect Mobile Traffic; Affects 5G Standard Too


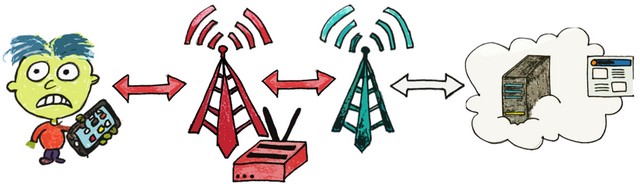
A squad of four researchers from the Ruhr-Academy in Bochum, Deutschland, and New York University Abu Dhabi in the UAE, have revealed that the 'data link layer' of LTE networks have at least three disquisitional vulnerabilities that could potentially allow attackers to non only eavesdrop on targets, but also direct users to hostile websites. The flaws are said to be built into the LTE standard itself, and bear on the second layer of LTE, known as the data link layer.
The research team, comprising of David Rupprecht, Katharina Kohls, Thorsten Holz, and Christina Pöpper, published the report in a research paper titled 'Breaking LTE Layer Ii', which will be presented at the 2019 IEEE Symposium on Security & Privacy in San Francisco. In the mean fourth dimension, they have already notified the GSMA and 3GPP about their findings.
What is 'aLTEr' and What Can information technology Practise?
According to the researchers, ii of the three attacks are passive, including an 'identity mapping attack' and a 'website fingerprinting attack'. While the first one allows hackers to silently assemble information about the victim(s), the second one allows the attacker to place the websites existence visited by an user on their LTE device.
The tertiary ane, meanwhile, is an agile assail dubbed 'change' "that allows an attacker to redirect network connections by performing DNS spoofing due to a specification flaw in the LTE standard".
Attacks Unlikely 'In a Real-World Scenario'
Thankfully, though, none of the attacks can exist employed widely past would-be hackers. That because, according to the researchers, the attacks require non only expensive and sophisticated equipment worth $4,000, merely also custom software, which means they are across the scope of a large majority of regular hackers effectually the world, but not across state-sponsored or corporate-backed teams.
To exploit the flaw, the attacker as well needs to be in physical proximity to their target(s), as information technology plain only works within a 1-mile radius.
"To acquit such attacks, the aggressor depends on specialized hardware (then chosen software-divers radios) and a customized implementation of the LTE protocol stack. In addition, a controlled environment helps to be successful within an acceptable amount of fourth dimension. In detail, the use of a shielding box helps to maintain a stable and racket-gratis connectedness to the attack setup. Especially the latter cannot be maintained in a real-world situation and more than applied science endeavor is required for real-world attacks"
Given all of the to a higher place, the researchers believe that "people of special interest such as politicians or journalists", are most likely to be the targets of such attacks, and non general users, even though there's reason to be cautious considering information technology also affects side by side-gen standards.
The Security Flaws Too Impact 5G
What's actually alarming is that the attack can also touch 5G networks. While the 5G standard does include additional security features, they are only optional at the moment. Co-ordinate to the researchers, the 5G standard will demand to incorporate the suggested security measures and employ stronger encryption at the data layer if its has to mitigate the vulnerability.
Source: https://beebom.com/critical-lte-security-flaws/
Posted by: yatesspareige.blogspot.com


0 Response to "Critical LTE Security Flaw Can Remotely Inspect Mobile Traffic; Affects 5G Standard Too"
Post a Comment